Sensing Driver Phone Use to Reduce Driver Distraction. Cell phone distractions have been a factor in high-profile accidents and are associated with a large number of automobile accidents. This project addresses the fundamental problem of distinguishing between a driver and passenger using a mobile phone, which is the critical input to enable numerous safety and interface enhancements for the driver distraction problem. We are building a detection system that leverages the existing car stereo infrastructure, e.g., the speakers and Bluetooth network. Our solution seeks to address major challenges including the complex multipath environment presented in the small confided space inside a car, minimizing interference between the speakers, and any sounds emitted should be unobtrusive to minimize distraction.
This project has received the Best Paper Award at the ACM International Conference on Mobile Computing and Networking (MobiCom) 2011.
Research News: The Wall Street Journal, MIT Technology Review, CNet, WCBS, Yahoo News, CSDN, Sohu and Sina.
Project Demonstration Video: Youtube

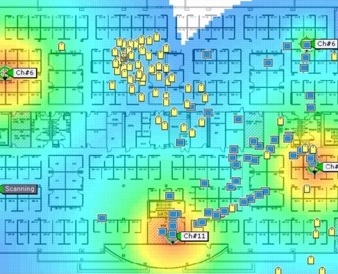
Mobile Healthcare Leveraging WiFi Network and Mobile Devices. Mobile devices and WiFi have become increasingly popular and gradually woven into our social lives. Smartphones equipped with powerful embedded sensors (e.g., accelerometers, GPS, microphones, and etc.) can be used to monitor multiple dimensions of human behaviors including physical, mental and social behaviors of wellbeing. The collected sensing data can thus be comprehensive enough to be mined not only for the understanding of human behaviors or daily life activities but also for supporting a broad range of mobile healthcare applications. We are designing a smartphone based secure healthcare monitoring system which allows users to be monitored for their mental, cognitive, and physical well-being and hence facilitate early diagnosis of potential illnesses and taking possible preventive measures. The communities extracted from a mobile phone enabled social network in our system can also be exploited for securing certain components of the system (e.g., coping with clone attacks). In addition, our low-cost system leverages the Channel State Information (CSI) extracted from WiFi signals on mobile devices to monitor vital signs and perform fine-grained sleep monitoring in home environments.
This project is partially funded by the National Science Foundation, PI: Yingying Chen.
Research News: Stevens News, Mobile Healthcare Information and Management Systems Society News, Mobile Health in Stevens, Fierce Mobile Healthcare, Digital Journal, MIT Technology Review, Yahoo News, Zeenews, MIT 科技评论, 网易科技, and 电子工程世界.
Project Demonstration Video: Youtube

Towards Understanding Smartphone User Privacy. This project focuses on addressing privacy concerns of smartphone users. In particular, it investigates how the usages of the smartphone applications (apps) may reshape users' privacy perceptions and what is the implication of such reshaping. There is only limited understanding on the consequences of user privacy losses, especially when large amount of privacy information leaked from smartphone users across many apps. We investigate how the mobile technology (i.e., smartphone and smartphone apps) can reveal users' personal information and identify the consequences of privacy violations, by taking users' social relationships into consideration. The project facilitates a deep understanding of user privacy in the age of mobile devices and further develops appropriate protective mechanisms. Smartphone user privacy across different levels are analyzed including individual, social and community relationships based on different levels of information leakage. Statistical models, such as Bayesian networks and hidden Markov models, are developed to understand users' temporal privacy leakage patterns based on experimental study.
This project is funded by the National Science Foundation, PI: Yingying Chen.
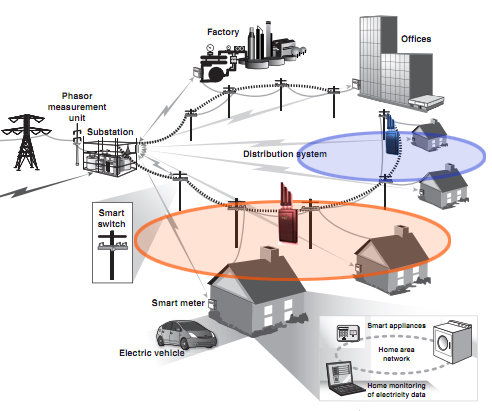
Building Self-Healing Smart Grid Under Jamming. A key component of a smart grid is its ability to collect useful information from a power grid for enabling control centers to estimate the current states of the power grid. Such information can be delivered to the control centers via wireless or wired networks. We envision that wireless technology will be widely used for local-area communication subsystems in the smart grid (e.g., in distribution networks). However, various attacks with drastic impacts can be launched in wireless networks such as channel jamming attacks and DoS attacks. In particular, jamming attacks can cause a wide range of damages to power grids, e.g., delayed delivery of time-critical messages can prevent control centers from properly controlling the outputs of generators to match load demands. We design a communication subsystem with enhanced self-healing capability under the presence of jamming through intelligent local controller switching. Our framework allows sufficient readings from smart meters to be continuously collected by various local controllers to estimate the states of a power grid under various attack scenarios. Additionally, we provide guidelines on optimal placement of local controllers to ensure effective switching of smart meters under jamming.
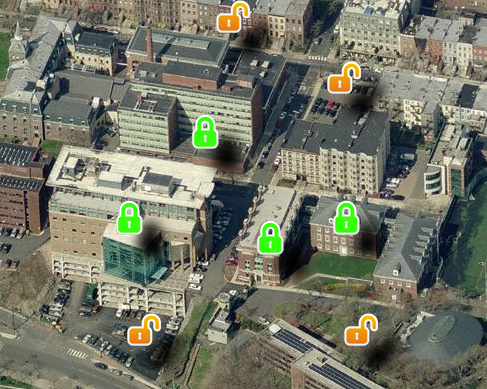
Exploiting Location as a New Dimension to Assist Wireless Security. As the increasingly pervasive wireless networks make it even easier to conduct attacks for new and rapidly evolving adversaries, the ubiquity of wireless is redefining security challenges. Thus, there is an urgent need to seek security solutions that can defend against attacks across the current heterogeneous mixes of wireless technologies. Location will be the cornerstone of new wireless services as future wireless services will support the access to resources and information from anywhere at anytime, implying that people will request services and information at different locations and at different times. In this project, we exploit location as a powerful information source to assist cryptographic-based methods to solve fundamental security problems such as detecting identity-based attacks and providing location-aware secure access of network resources.
This project is funded by the National Science Foundation, PI: Yingying Chen.

Utilizing Physical Layer Properties for Secret Key Extraction in Mobile Environments. Information sharing and various data transactions on wireless devices have become an inseparable part of our daily lives. However, securing wireless communication remains challenging in dynamic mobile environments due to the shared nature of wireless medium and lacking of fixed key management infrastructures. Generating secret keys using physical layer information thus has drawn much attention to complement traditional cryptographic-based methods. This project is designing schemes of secret key generation among wireless devices using physical layer information of radio channel such as the Received Signal Strength (RSS) and the Channel State Information (CSI). We currently are focusing on exploring the fine-grained physical layer information (i.e., CSI) from multiple subcarriers of Orthogonal Frequency-Division Multiplexing (OFDM) to achieve higher secret bit generation rate and make the secret key extraction approaches (based on physical-layer characteristics) more practical.
This project is partially supported Army Research Office, PI: Yingying Chen.

Securing Spectrum Usage in Future Radio Systems. The openness of the lower-layer protocol stacks renders cognitive radios (CR) an appealing solution to dynamic spectrum access (DSA). Its open nature will increase the flexibility of spectrum utilization and promote spectrally-efficient communication. Nevertheless, due to the exposure of the protocol stacks to the public, CR platforms can become a tempting target for adversaries or irresponsible secondary users. A misuse of a CR can significantly compromise the benefits of DSA and threaten the privileges of incumbent users. Therefore, having the ability to enforce spectrum etiquettes is critical in future radio systems. We are designing efficient mechanisms, and developing effective frameworks that can both detect anomalous activities in spectrum usage as well as localize adversaries without requiring overhead on wireless devices.
This project is funded by the National Science Foundation, PI: Yingying Chen.